Organizations today face an expanding digital battlefield where every connected device represents a potential entry point for attackers. From laptops and smartphones to servers and IoT devices, the attack surface has grown dramatically, making robust protection strategies more critical than ever. Endpoint security solutions have emerged as the frontline defense, combining advanced threat detection, real-time monitoring, and automated response to neutralize threats before they escalate into full-scale data breaches. As cyber adversaries grow more sophisticated, businesses of every size must invest in layered, intelligent security frameworks that evolve alongside the threat landscape.
What Are Endpoint Security Solutions?
Endpoint security solutions are integrated platforms designed to monitor, detect, and respond to threats targeting individual devices connected to a corporate network. Unlike traditional antivirus tools, modern solutions leverage AI-powered security engines and behavioral analytics to identify both known and unknown threats.
- They protect desktops, laptops, mobile devices, and servers from malware, ransomware, and phishing attacks.
- They provide centralized visibility across all endpoints through a unified management console.
- They integrate with broader security ecosystems including SIEM platforms and Zero Trust Architecture frameworks.

Why Endpoint Threats Have Become More Complex
The modern threat landscape has shifted dramatically due to remote work adoption, cloud migrations, and the explosion of connected IoT devices. Cybercriminals now deploy multi-stage attacks that blend social engineering with zero-day threats to bypass conventional defenses.
- Ransomware campaigns have evolved to include double extortion tactics, encrypting data while threatening public exposure.
- Phishing attacks are increasingly personalized, targeting specific employees with convincing lures.
- Supply chain compromises allow attackers to infiltrate organizations through trusted third-party software vendors.
The Role of EDR in Modern Defense
Endpoint Detection and Response (EDR) is a cornerstone technology within endpoint security solutions, providing continuous monitoring and forensic-level visibility into device activity. EDR tools record behavioral telemetry, enabling security teams to trace the origin and spread of an attack.
- EDR platforms correlate events across endpoints to detect lateral movement and privilege escalation.
- They support threat hunting by allowing analysts to query historical data and identify hidden compromises.
- Integration with threat intelligence feeds ensures detection rules stay updated against emerging attack techniques.
Next-Generation Antivirus and AI-Powered Protection
Traditional signature-based antivirus cannot keep pace with the volume and novelty of modern threats. Next-Generation Antivirus (NGAV) replaces outdated models with machine learning algorithms that analyze file behavior, memory activity, and process execution patterns in real time.
- NGAV detects fileless malware that operates entirely in memory, leaving no trace on disk.
- AI/ML threat detection engines adapt automatically to new attack variants without requiring manual signature updates.
- These tools reduce false positive rates, allowing security teams to focus on genuine incidents rather than chasing noise.
Mobile Device Management and Endpoint Control
Mobile Device Management (MDM) extends endpoint security solutions to smartphones, tablets, and other portable assets. As employees access sensitive corporate data from personal or managed mobile devices, MDM ensures consistent policy enforcement across the board.
- MDM platforms enforce encryption, screen lock policies, and remote wipe capabilities on lost or stolen devices.
- They control which applications can be installed, reducing exposure to malicious or unauthorized software.
- Integration with identity management systems ensures only authenticated users access corporate resources.
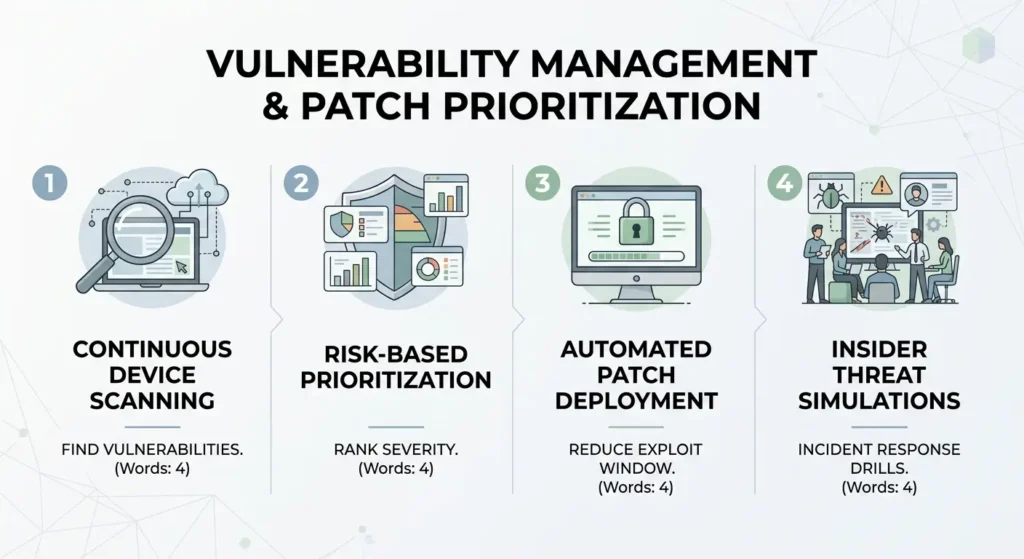
Vulnerability Management and Patch Prioritization
Unpatched software remains one of the most exploited vectors for attackers. Effective endpoint security solutions incorporate automated vulnerability management to continuously scan devices and prioritize remediation based on risk severity.
- Automated patch deployment reduces the window between vulnerability disclosure and exploitation.
- Risk-based prioritization ensures critical vulnerabilities receive immediate attention while lower-risk issues are scheduled accordingly.
- Continuous scanning identifies misconfigurations and outdated software that attackers commonly target.
Cloud-Based Security and Scalable Endpoint Defense
Cloud-based security architectures allow organizations to extend endpoint protection across distributed workforces without relying on on-premises infrastructure. Cloud-delivered endpoint security solutions offer rapid deployment, automatic updates, and centralized policy management from any location.
- Cloud platforms process threat intelligence at scale, correlating data from millions of endpoints to identify emerging attack patterns.
- They reduce infrastructure overhead by eliminating the need for local servers dedicated to security management.
- Scalability allows organizations to onboard new devices instantly, ensuring consistent protection regardless of workforce size.
Zero Trust Architecture and Endpoint Verification
Zero Trust Architecture operates on the principle of “never trust, always verify,” requiring every device and user to authenticate continuously before accessing network resources. When integrated with endpoint security solutions, Zero Trust minimizes the blast radius of any successful compromise.
- Device health checks verify that endpoints meet security baselines before granting access to sensitive applications.
- Micro-segmentation limits lateral movement, containing breaches to isolated network segments.
- Continuous authentication challenges ensure that compromised credentials cannot be exploited for persistent access.
Network Security Integration and Threat Correlation
Endpoint protection does not function in isolation; it must connect seamlessly with broader network security infrastructure. When administrators configure integrations, they can simply paste here the relevant API tokens or configuration scripts into the SIEM platform to unify event correlation across the environment.
- SIEM platforms aggregate endpoint telemetry with network logs, cloud activity, and user behavior data for holistic threat analysis.
- Automated playbooks trigger response actions such as isolating infected endpoints or blocking malicious IP addresses.
- Threat intelligence sharing between endpoint agents and network firewalls accelerates the identification of coordinated attack campaigns.
Incident Response and Recovery Capabilities
The ability to respond swiftly and recover effectively is as important as prevention. Modern endpoint security solutions embed incident response workflows directly into their platforms, reducing mean time to remediation.
- Automated containment isolates compromised devices from the network within seconds of detecting a confirmed threat.
- Forensic investigation tools capture memory snapshots and process trees, accelerating root cause analysis.
- Recovery features restore affected systems to a known-good state, minimizing business disruption after a ransomware or malware incident.
Conclusion
Building a resilient defense against modern cyber threats demands more than point solutions; it requires an integrated, intelligence-driven strategy that covers prevention, detection, response, and recovery across every device in the organization. Endpoint security solutions serve as the foundation of that strategy, combining EDR, NGAV, MDM, cloud-based security, and Zero Trust principles into a unified defense fabric. As cybersecurity threats continue to evolve in sophistication and scale, organizations that invest in comprehensive, adaptive endpoint protection will be best positioned to safeguard their data, operations, and reputation in an increasingly hostile digital environment.
Frequently Asked Questions
What are endpoint security solutions and why are they important?
Endpoint security solutions are platforms that protect devices such as laptops, smartphones, and servers from cyber threats including malware, ransomware, and phishing. They are important because every connected device represents a potential entry point for attackers, and a single unprotected endpoint can compromise an entire network.
How does EDR differ from traditional antivirus software?
EDR (Endpoint Detection and Response) goes far beyond traditional antivirus by providing continuous behavioral monitoring, forensic investigation capabilities, and automated threat response. While traditional antivirus relies on known malware signatures, EDR detects anomalous behavior and zero-day threats that have no prior signatures.
Can endpoint security solutions protect against ransomware attacks?
Yes, modern endpoint security solutions use behavioral analysis, process monitoring, and AI-powered threat detection to identify ransomware activity before encryption begins. Features like automated isolation and rollback capabilities also help organizations recover quickly when an attack does occur.
What is the role of Zero Trust Architecture in endpoint security?
Zero Trust Architecture ensures that no device or user is automatically trusted, requiring continuous verification of identity and device health before granting access to resources. When combined with endpoint security solutions, it significantly reduces the risk of lateral movement following a breach.
How do cloud-based endpoint security solutions benefit remote workforces?
Cloud-based endpoint security solutions protect remote employees regardless of location by delivering real-time threat intelligence, policy enforcement, and centralized management through the cloud. They eliminate the need for VPN-dependent, on-premises security infrastructure while ensuring consistent protection across all endpoints.
