Every time you type a website address into your browser, the Domain Name System (DNS) silently converts that domain name into a machine-readable IP address. This foundational process enables seamless internet navigation but remains highly vulnerable to manipulation. DNS spoofing is a sophisticated cyberattack that corrupts this resolution process, redirecting users to fraudulent websites without triggering any visible security warning. Understanding how this attack operates is essential for IT professionals, businesses, and everyday users committed to strong network security in an increasingly hostile digital environment.
What Is DNS Spoofing?
DNS spoofing, also referred to as DNS cache poisoning, is a cyberattack in which an attacker injects forged DNS records into a resolver’s cache. This manipulation causes the resolver to return a false IP address, sending users to malicious websites instead of their intended destination.
- It exploits the trust embedded in the DNS resolution process
- Attackers require no direct access to the victim’s device
- Both individual users and enterprise networks can be targeted
- Redirection occurs without any visible security alert to the end user
How the Domain Name System Operates
The Domain Name System functions as the internet’s address book. When a user queries a domain, recursive resolvers search through a hierarchy of authoritative name servers to retrieve the matching IP address, then cache the result to speed up future lookups.
- Recursive resolvers process DNS queries on behalf of the user
- Authoritative name servers store verified, official DNS records
- Cached records carry a Time-To-Live (TTL) value that controls their lifespan
- This caching mechanism improves speed but introduces exploitable security gaps
Step-by-Step Attack Mechanics
The attack unfolds at the network level, exploiting the way resolvers accept and store responses. The sequence is rapid, highly targeted, and leaves minimal forensic traces.
- The attacker monitors network traffic and detects an outgoing DNS query
- Forged response packets containing a false IP address are dispatched to the resolver
- The resolver, lacking strong authentication, accepts and caches the fraudulent record
- All subsequent users querying that resolver are silently redirected to the attacker’s server
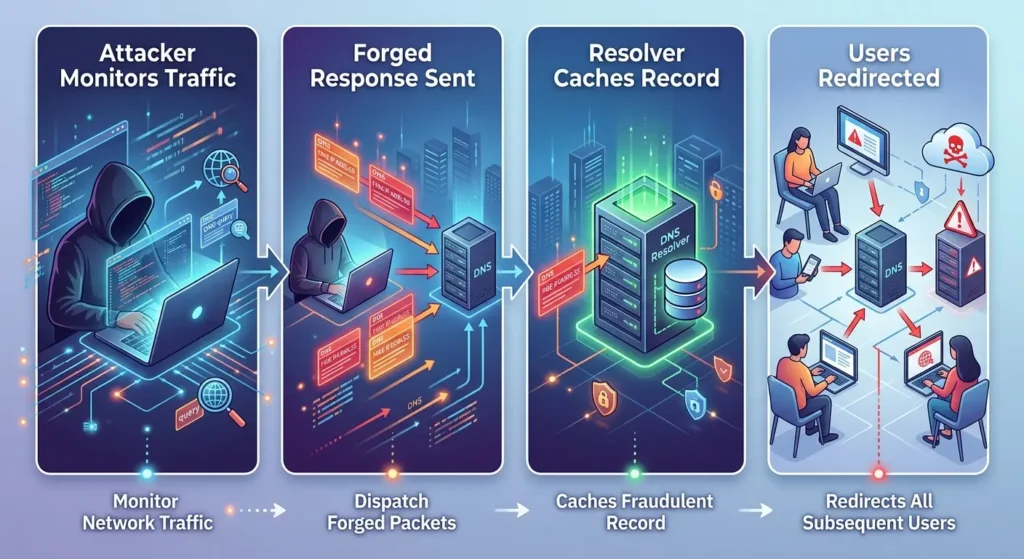
DNS was originally designed for speed and operational efficiency, not for robust authentication, making it inherently susceptible to response injection.
Understanding DNS Cache Poisoning
DNS cache poisoning is the foundational technique behind most DNS spoofing attacks. It corrupts the cached records held by recursive resolvers, ensuring that false IP address mappings persist until the TTL expires or the cache is manually cleared.
- Attackers exploit weak transaction ID validation in older DNS implementations
- A single poisoned resolver can misdirect thousands of simultaneous users
- Corrupted records remain active for the full TTL duration
- Randomized source ports and query IDs in modern systems reduce but do not eliminate this risk
Common Types of DNS-Based Cyberattacks
DNS manipulation takes several distinct forms, each targeting a different vulnerability within the resolution chain. Recognizing these variations is fundamental to building comprehensive network defenses.
- Kaminsky Attack: Floods a resolver with rapid queries to inject poisoned records before a legitimate response arrives
- Pharming: Redirects large volumes of traffic from legitimate websites to fraudulent ones at scale
- DNS Hijacking: Directly alters DNS settings on a router, device, or hosting account
- BGP Hijacking: Manipulates routing tables to intercept DNS traffic at a broader infrastructure level
Man-in-the-Middle Attacks and Packet Interception
A man-in-the-middle (MITM) attack allows an attacker to intercept DNS queries in transit and replace authentic server responses with forged ones. This variant of DNS spoofing is especially effective on unsecured public Wi-Fi networks where traffic flows without encryption.
- The assailant situates themself amid the client and the DNS server.
- Intercepted DNS packets are swapped with spoofed responses containing a false IP address
- Victims connect to the attacker’s server believing it to be the authentic destination
- Credentials, session tokens, and private communications are harvested without detection
Phishing Risks Enabled by DNS Manipulation
DNS spoofing creates optimal conditions for phishing attacks by silently directing users to convincing replicas of trusted websites. Once on a fraudulent page, users may voluntarily submit sensitive information without suspicion.
- Fake sites often replicate the exact visual design of banking or e-commerce platforms
- Attackers can obtain SSL certificates that make spoofed sites appear fully secure
- Users may enter passwords, financial details, or personal identification without hesitation
- These attacks are nearly impossible to detect without dedicated DNS monitoring tools
How Recursive Resolvers Become Targets
Recursive resolvers are high-value targets because they serve large user populations and cache responses centrally. Compromising a single resolver produces far-reaching impact across every user it serves.
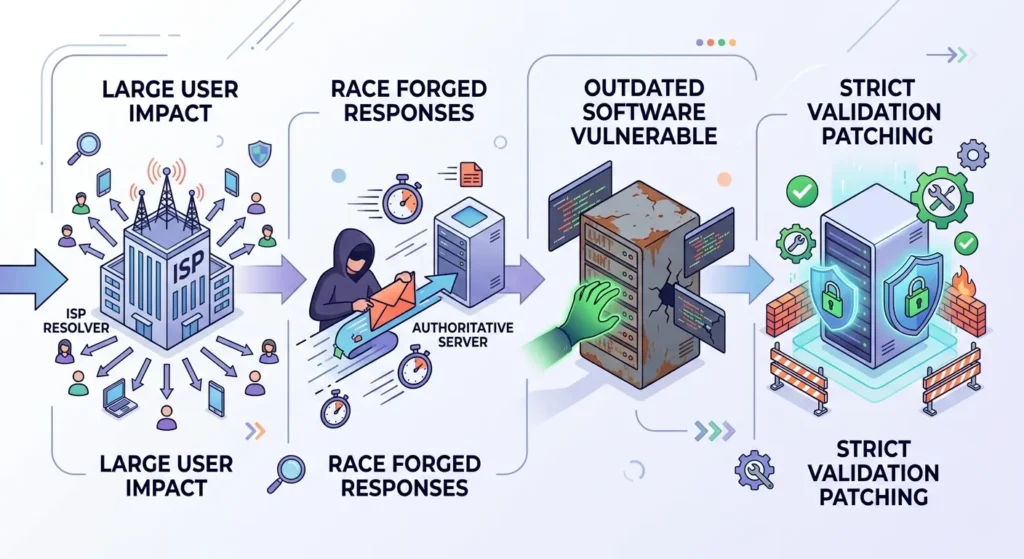
- ISP-operated resolvers serve millions of users, amplifying the scope of each successful attack
- Attackers race to deliver forged responses before the legitimate authoritative server replies
- Resolvers running outdated software remain especially vulnerable to injection attempts
- Strict query validation and frequent security patching are essential protective practices
DNSSEC and Cryptographic Authentication
DNSSEC (Domain Name System Security Extensions) adds a layer of cryptographic authentication to the resolution process, allowing resolvers to verify that records have not been altered during transmission. It is among the most direct and effective defenses against DNS spoofing at the resolver level.
- DNSSEC attaches digital signatures to DNS records at every zone level
- A verifiable chain of trust extends from the root zone down to individual domain records
- Resolvers check these cryptographic signatures before accepting and caching a response
- DNSSEC validates record integrity but does not encrypt the DNS queries themselves
Encrypted DNS Protocols That Strengthen Security
Beyond DNSSEC, several encrypted DNS protocols help shield the resolution process from interception and manipulation at the transport layer.
- DNS-over-HTTPS (DoH): Encapsulates DNS queries within HTTPS traffic, blocking interception by third parties
- DNS-over-TLS (DoT): Wraps DNS communication in a TLS encrypted tunnel for transport-level security
- Response Rate Limiting (RRL): Restricts response rates to slow down flooding and injection attempts
- QNAME minimization: Limits data shared with authoritative servers, reducing the attack surface during each lookup
Proactive Security Measures to Reduce Exposure
Organizations and individuals can take targeted steps to significantly reduce their vulnerability to DNS-based attacks before any incident occurs.
- Enable DNSSEC validation on all managed domains and resolvers
- Deploy DoH or DoT to encrypt all outgoing DNS query traffic
- Regularly audit and flush DNS caches to remove potentially poisoned records
- Configure intrusion detection systems to flag anomalous DNS query patterns
- Maintain updated DNS server software to eliminate known vulnerability windows
Conclusion
DNS spoofing poses a persistent, technically sophisticated cybersecurity threat targeting the core layer of internet communication. By exploiting cached DNS records and resolver authentication flaws, attackers redirect users, fuel phishing campaigns, and intercept sensitive data at scale. Defending against these cybersecurity risks demands a layered strategy blending DNSSEC, encrypted DNS protocols, ongoing network monitoring, and routine security audits. Organizations grasping the intricacies of DNS manipulation stand best equipped to safeguard their infrastructure and users from advancing cyber threats.
Frequently Asked Questions
What is the primary objective of DNS spoofing?
The core aim of DNS spoofing is to redirect users from legitimate websites to malicious ones, enabling credential theft, malware distribution, or unauthorized interception of sensitive information without the victim’s knowledge.
Is DNS spoofing the same as DNS cache poisoning?
DNS cache poisoning is the specific technique used to execute DNS spoofing. Poisoning corrupts resolver cache records, which is the method; spoofing describes the broader attack outcome that ultimately affects end users.
How does DNSSEC protect against DNS attacks?
DNSSEC applies cryptographic digital signatures to DNS records at each zone level, allowing resolvers to verify that responses have not been tampered with during transmission before they are cached and served to users.
Can HTTPS protect users from DNS-based redirection?
HTTPS secures data after a connection is established but does not prevent malicious redirection at the DNS layer. Protocols like DNS-over-HTTPS (DoH) and DNS-over-TLS (DoT) address the DNS query itself, providing more direct protection.
What are the warning signs of a DNS attack?
Common indicators include unexpected website redirects, SSL certificate warnings on familiar domains, unfamiliar IP addresses appearing in DNS logs, and noticeably slower page load times on sites you visit regularly.
