Post-exploitation in cybersecurity is the phase that determines how severe a breach ultimately becomes. This blog covers the full post-exploitation lifecycle, from initial situational awareness to privilege escalation, lateral movement, and data exfiltration. It examines the tools and tactics attackers use at each stage, how ethical hackers simulate these techniques during penetration testing, and the detection and prevention strategies security teams must deploy. By the end, readers will understand what happens inside a network after an attacker gains access and exactly how to stop it.
Why Post-Exploitation in Cybersecurity Defines the True Cost of a Breach
The average attacker spends 207 days inside a compromised network before being detected. Initial access is only the starting point. Post-exploitation in cybersecurity refers to every action an attacker takes after that first foothold is established and this is where the catastrophic damage occurs.
Unlike the initial intrusion, which often relies on a single vulnerability or phishing lure, post-exploitation is methodical, layered, and specifically designed to evade detection. Attackers escalate privileges, harvest credentials, move laterally across systems, plant persistent backdoors, and exfiltrate sensitive data all while masquerading as normal network activity.
This blog breaks down each stage of the post-exploitation phase, the real-world tools threat actors deploy, how ethical hackers use identical techniques to expose weaknesses before criminals do, and the concrete steps every organization must take to detect and disrupt post-exploitation activity at its earliest stage.
Key Stages of Post-Exploitation in Cybersecurity
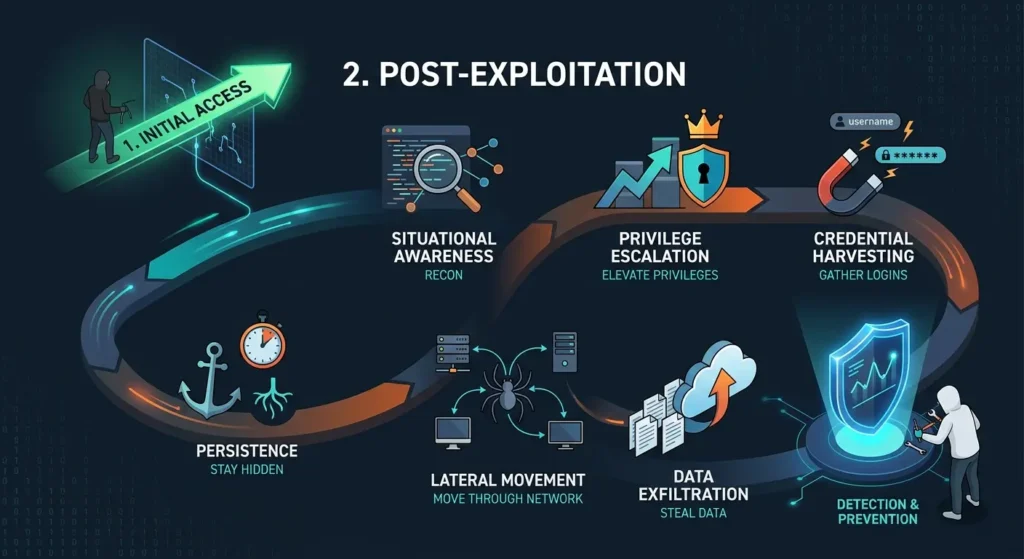
The post-exploitation phase in cybersecurity follows a deliberate, sequential attack chain. Each stage builds on the previous one, deepening the attacker’s position and making remediation increasingly difficult. Understanding this progression is foundational for building effective defenses.
- Situational awareness: Attackers enumerate the compromised host identifying the OS version, installed software, active processes, and network configuration to map their environment.
- Privilege escalation: Low-privileged access is elevated to administrator or root level using misconfigurations, unpatched vulnerabilities, or stolen credentials.
- Credential harvesting: Tools like Mimikatz extract plaintext passwords, NTLM hashes, and Kerberos tickets directly from system memory.
- Lateral movement: Stolen credentials and protocols such as RDP, SMB, and WMI enable attackers to pivot from the initial system to high-value targets across the network.
- Persistence establishment: Backdoors, scheduled tasks, registry modifications, and rogue accounts ensure continued access even after the original entry point is closed.
- Data exfiltration: Sensitive files and intellectual property are staged and transmitted to attacker-controlled servers using encrypted or covert channels.
Each stage amplifies attacker leverage and reduces the defender’s ability to achieve full remediation.
Proven Privilege Escalation Techniques Used in Post-Exploitation Attacks
Privilege escalation is among the most consequential steps in post-exploitation cybersecurity. It converts a limited foothold into domain-level control, unlocking nearly every subsequent attacker objective. Attackers pursue two paths: vertical escalation (higher privileges on one system) and horizontal escalation (equivalent access across more systems).
- Unpatched OS vulnerabilities: Exploits targeting known CVEs such as CVE-2021-4034 on Linux grant root or SYSTEM privileges directly without requiring additional credentials.
- Misconfigured sudo rules: Overly permissive sudo configurations on Linux allow standard users to execute administrative commands with no password required.
- Token impersonation: On Windows, tools like Incognito steal access tokens from privileged processes and use them to execute commands at higher permission levels.
- DLL hijacking: Malicious DLL files placed in application search directories execute with the elevated privileges of the calling process.
- Password reuse exploitation: Credentials harvested from one account routinely unlock administrator accounts due to widespread reuse across enterprise environments.
Applying the principle of least privilege, enforcing aggressive patch cycles, and conducting regular permission audits are the primary defenses against these escalation techniques.
Essential Lateral Movement Techniques Attackers Use After a Breach
Lateral movement is how attackers navigate from an initial compromise to higher-value systems across the same network. It is a defining characteristic of advanced persistent threats and a core element of post-exploitation cybersecurity operations.
- Pass-the-Hash (PtH): Captured NTLM password hashes authenticate attackers to remote systems without ever requiring the plaintext password.
- Pass-the-Ticket (PtT): Kerberos tickets stolen from memory allow attackers to authenticate as legitimate users across Active Directory domains.
- EternalBlue exploitation: The SMB vulnerability underlying WannaCry enables remote code execution on unpatched Windows systems without credentials.
- RDP session hijacking: Attackers take control of existing Remote Desktop sessions belonging to logged-in users, bypassing new login event generation.
- Living-off-the-land (LOLBin) abuse: Native tools including PowerShell, WMI, and PsExec execute attacker commands on remote systems while blending into legitimate administrative traffic.
Detecting lateral movement requires network segmentation, behavioral analytics platforms, and continuous monitoring of authentication logs for anomalies such as off-hours logins and unexpected remote connections.
Effective Data Exfiltration and Persistence Methods in Post-Exploitation
Data exfiltration and persistence are the two outcomes attackers most prioritize during the post-exploitation cybersecurity phase. Once deep access is secured, the focus shifts to extracting value and ensuring continued access even if portions of the compromise are discovered.
- DNS tunneling: Stolen data is encoded within DNS query strings and transmitted using a protocol most firewalls do not inspect, making exfiltration nearly invisible.
- HTTPS exfiltration: Sensitive data travels over encrypted HTTPS connections to attacker-controlled domains, bypassing traditional content inspection tools.
- Scheduled tasks and cron jobs: Malicious scheduled tasks on Windows or cron jobs on Linux silently re-establish attacker access at regular intervals.
- Registry Run key persistence: Malware entries embedded in Windows registry Run keys execute automatically at startup without any user interaction.
- Rogue administrative accounts: Hidden local or domain accounts created by attackers maintain access long after the original compromise vector is remediated.
Data loss prevention (DLP) solutions, DNS traffic monitoring, and systematic audits of scheduled tasks and privileged accounts are critical controls for disrupting these mechanisms.
How Ethical Hackers Simulate Post-Exploitation in Cybersecurity Engagements
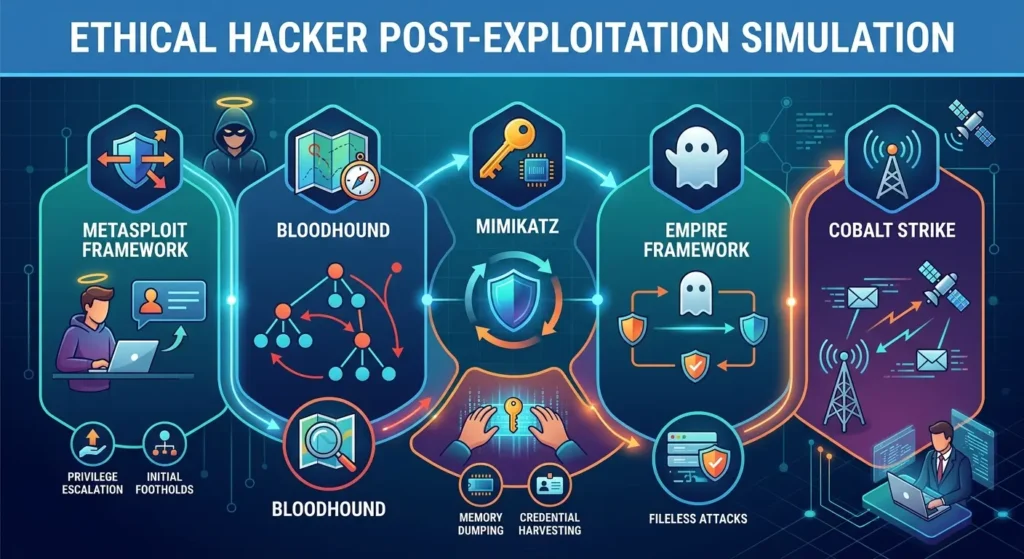
Ethical hackers deliberately replicate post-exploitation in cybersecurity environments to surface vulnerabilities before malicious actors can weaponize them. Full-scope penetration tests that include post-exploitation simulation deliver dramatically greater security value than assessments limited to initial access only.
- Metasploit Framework: Post-exploitation modules simulate privilege escalation, credential dumping, and lateral movement within controlled testing engagements.
- Cobalt Strike: A commercial red team platform that replicates advanced persistent threat behavior, including beacon-based command-and-control (C2) communication.
- BloodHound: Maps Active Directory environments to expose the shortest privilege escalation and lateral movement paths available to an attacker.
- Mimikatz: Demonstrates real credential harvesting risks and validates whether in-memory password protections are functioning as intended.
- Empire Framework: Simulates fileless attack techniques and tests endpoint detection and response (EDR) capabilities against post-exploitation tradecraft.
Organizations that commission red team exercises inclusive of the full post-exploitation lifecycle gain the clearest picture of their true security posture.
Frequently Asked Questions About Post-Exploitation in Cybersecurity
- What is post-exploitation in cybersecurity?
Post-exploitation in cybersecurity refers to all attacker activity that occurs after initial access to a system or network is established. This includes privilege escalation, lateral movement, credential harvesting, persistence establishment, and data exfiltration the phases where the most severe breach damage occurs. - What tools do attackers commonly use during the post-exploitation phase?
Attackers frequently use Mimikatz for credential harvesting, Cobalt Strike for C2 infrastructure, BloodHound for Active Directory attack path mapping, and native system tools like PowerShell and WMI to execute commands without deploying detectable malware. - How can organizations detect post-exploitation activity on their networks?
Effective detection relies on behavioral analytics, SIEM correlation rules, EDR platforms, and authentication log monitoring. Indicators include unusual account activity, off-hours remote logins, new scheduled tasks, and unexpected lateral connections between internal systems. - What is the difference between lateral movement and privilege escalation?
Privilege escalation means gaining higher permission levels on a single compromised system. Lateral movement means using existing credentials and access to compromise additional systems across the network. Both are sequential stages within the post-exploitation phase. - Why is post-exploitation more damaging than the initial breach?
The initial breach provides access; post-exploitation maximizes the damage from that access. Attackers entrench themselves, exfiltrate sensitive data, compromise additional systems, and establish persistence making detection and full remediation significantly more complex and costly.
Conclusion: Building a Defense Against Post-Exploitation in Cybersecurity
A single compromised credential can become a full organizational breach when post-exploitation goes undetected. Attackers move through privilege escalation, lateral movement, persistence, and exfiltration with precision and they count on defenders being focused only on perimeter security. Combating post-exploitation in cybersecurity demands a layered strategy built on least-privilege access, aggressive patch management, network segmentation, continuous behavioral monitoring, and regular red team exercises that simulate the full attack lifecycle.
Security teams must operate under a breach-assumption mindset not just preventing initial access, but detecting and disrupting attacker activity the moment it begins inside the network. Audit your environment for post-exploitation risks today. Deploy EDR solutions, map your Active Directory attack paths using BloodHound, and run a comprehensive red team engagement that tests your organization’s ability to detect and contain each stage of the post-exploitation chain.
