Zero Trust Security- In our always-on digital world, hackers hit hard and fast, slipping through tiny gaps in defenses. Old-school “trust once you’re in” setups can’t handle today’s nasty attacks like ransomware, sneaky insiders, or risks from folks working remotely. That’s where zero trust security comes in—it figures a break-in is bound to happen and checks every single request non-stop. This straightforward guide breaks down it from the basics to putting it into action, so you can toughen up against whatever’s coming next.
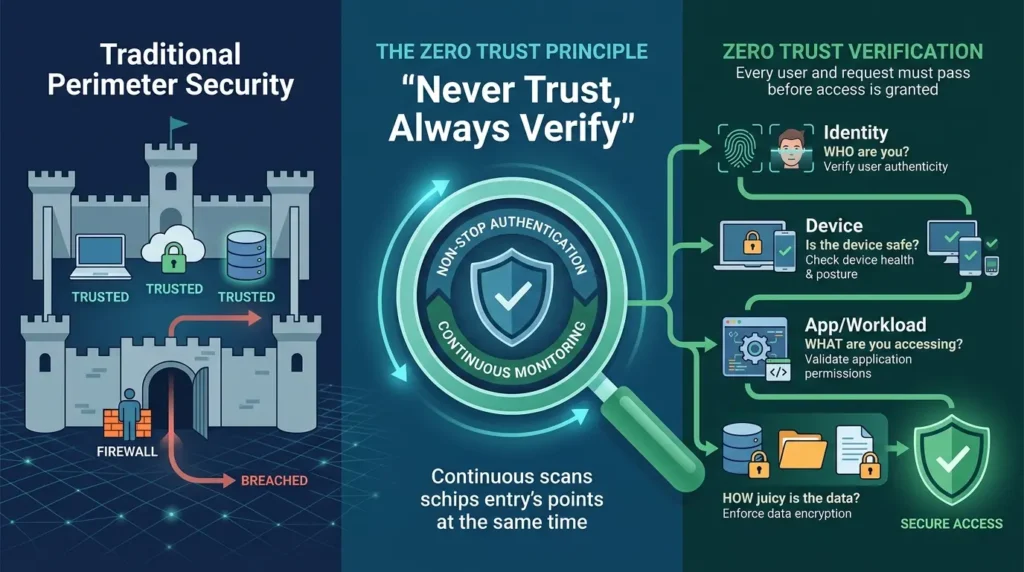
This trust security flips the script on protecting networks by ditching any automatic trust. Forget those old perimeter walls that let you roam free once past the gate. Zero trust security lives by “don’t trust anyone, check everything.” Users, gadgets, apps, and data bits all get grilled, no matter where they are
Picture a bank vault where even staff punch in codes, scan eyes, and solve riddles for each safe. This security trust does that online. John Kindervag from Forrester cooked it up in 2010, and it blew up with cloud shifts and everyone working from home. Companies use it to see the whole network as enemy ground, with rules that flex based on things like how someone acts, if their device is healthy, or how juicy the data is.
Zero trust security moves away from fixed walls to smart checks tied to who you are. It shines in mixed setups where people grab stuff from home laptops, phones, or outside clouds. The big win? It keeps damage small if something slips through.
Why Outdated Security Models Struggle Against Modern Threats
Old defenses worked like a castle with a moat—lock down the outside, and inside is golden. Firewalls, VPNs, and virus scanners watched incoming stuff, betting the inner network was fine. But that’s not reality anymore.
Take the 2020 SolarWinds mess—bad guys hid in legit software updates, spying on big companies for months. Or Log4Shell in 2021, one tiny code bug that cracked open millions of machines. Then remote work surged after the pandemic, with people logging in from sketchy coffee shop Wi-Fi.
Here’s why those old ways fall short:
- Network edges vanish with cloud apps and online services.
- Once you’re in (even if hacked), insiders wander anywhere.
- Attack spots explode from smart gadgets, APIs, and sneaky unauthorized tech.
Zero trust security plugs these holes by saying no to blind faith. It carves networks into tiny zones, stopping hackers from jumping around—a move in 80% of breaks, says Verizon’s DBIR. With average hacks costing $4.45 million (IBM 2023), zero trust security fights back by planning for the worst right away.
Key Foundations of the Zero Trust Security
Framework
It builds on seven key ideas from NIST SP 800-207. They shape every choice to keep things locked tight.
- Verify explicitly: Check identity, device state, spot, and timing every time. No shortcuts.
- Least privilege access: Hand out just enough power, just for the moment needed.
- Assume breach: Build like hackers are already inside. Watch non-stop and wall off spots fast.Yank it if something’s off
- All entities equal risk: People, servers, smart bulbs—nothing gets a pass. Scan it all hard.
- Context-aware: Weigh clues like odd login times or location jumps.
- Multi-factor everywhere: Stack biometrics, keys, and habit tracking on top of passwords
- Automation drives scale: Humans can’t keep up; smart tools handle the heavy lifting.
These rules turn security from fixing holes after the fact to blocking trouble upfront
How This Works in Modern IT
Environments
The security trust layers checks across cloud, on-site, and blended systems. Think of cops at every corner, flashing IDs before anyone moves.
- First, prove who you are with tools like Okta or Azure ADMFA and risk checks included.
- Next, scan the device: Patches up? Antivirus running? Encrypted?
- Then policy deciders like Zscaler or Palo Alto Prisma weigh the full picture.
- Tiny network slices from stuff like Illumio block side-to-side creeps.
- Data stays wrapped in TLS encryption; DLP marks secrets.
- Logs feed into SIEM like Splunk or Elastic for round-the-clock watching and lockdowns.
Say a coder wants repo access from their laptop. Zero trust security pings identity, device okayness, normal habits, and data value—greenlight a sliver or shut it down. Remote teams love it; Google’s BeyondCorp ditched VPNs for 100,000+ staff.
Key Components of a Zero Trust Architecture
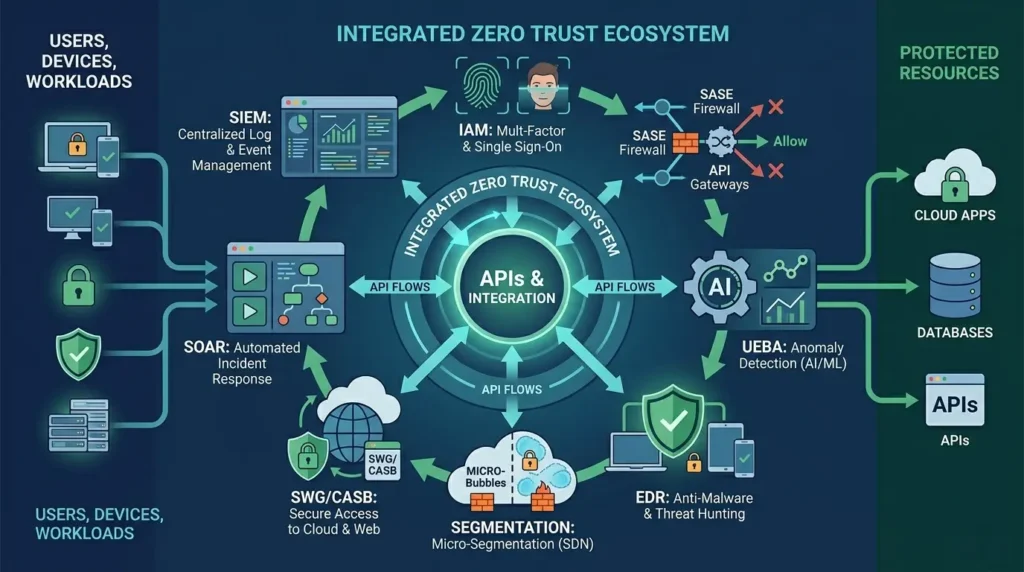
It ties these pieces into one smooth system.
- Identity and Access Management (IAM): The front door with single sign-on, MFA, and tight admin controls (think SailPoint)
- Security Policy Enforcement Points (PEPs): Firewalls or SASE that block or allow on the fly
- User and Entity Behavior Analytics (UEBA): Machine learning spots weird moves.
- Endpoint Detection and Response (EDR): CrowdStrike-style watchers on devices.
- Network segmentation tools: SDN splits everything into safe bubbles.
- Secure Web Gateways (SWG) and CASBs: Vet web and cloud flows.
- SIEM and SOAR: Pull logs, fire off auto-fixes.
They link via APIs, flexing for fast dev teams or far-flung computing.
Benefits of Implementing
Switching to zero trust security pays off big against growing dangers.
- Shrink breach damage: Walls keep it local; Mandiant says 50% quicker shutdowns.
- See everything: Logs light up dark corners, nailing rules like GDPR or HIPAA
- Easy remote work: No VPN jams for spread-out teams.
- Save cash: Ditch bloated edges for smart focus—Gartner sees 50% OpEx cuts.
- Speedy fixes: Auto-tools drop response from days to minutes.
- Keep business humming: Survives chain attacks, unlike Colonial Pipeline’s 2021 shutdown.
India’s firms dodge 1.3 million daily hits (CERT-In 2023) with the trust security’s edge.
Common Challenges in Adoption Zero Trust
Security
- Jumping to zero trust security means shaking up habits and tech.
- Old apps won’t play nice with splits; full swaps cost a bundle.
- Hidden tech flies under radar, messing up rules.
- Teams lack know-how in access tools, bots, and data crunching.
- Users hate pop-up checks; bosses eye startup bills ($1-5M for midsize).
- Sloppy lists leave gaps.
Ease in: Test on key apps first.
Zero Trust Security vs Traditional Security
| Aspect | Traditional Security | Zero Trust Security |
| Trust Model | Trust inside perimeter | Never trust, always verify |
| Access Control | Broad, network-based | Granular, identity-centric |
| Threat Assumption | External only | Internal and external |
| Scalability | VPN-limited | Cloud-native, unlimited |
| Breach Impact | Lateral movement easy | Contained via segmentation |
Trust security rules fluid setups; old ways fit locked-down, offline spots.
Best Practices for Implementing Zero Trust Security
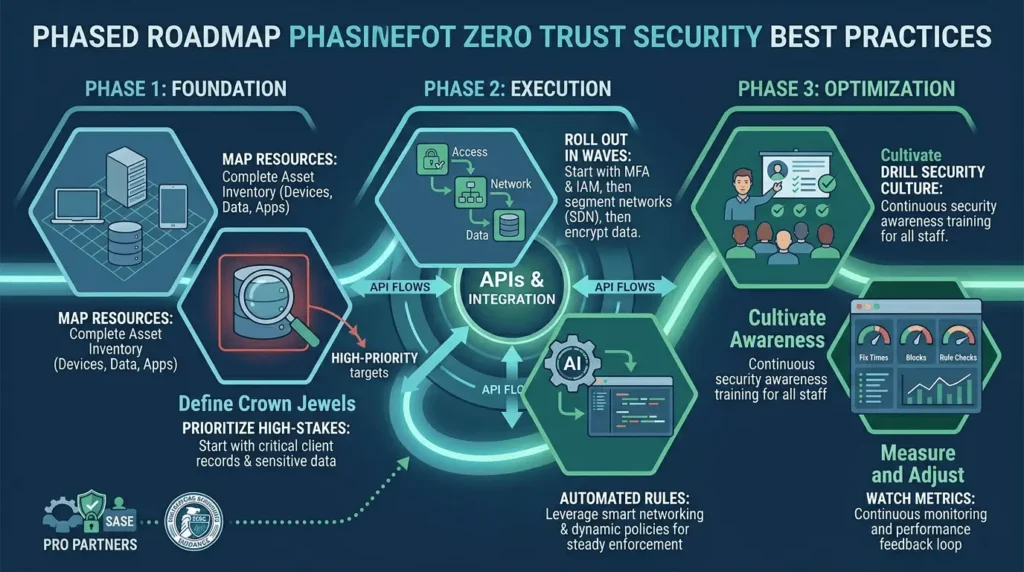
- Nail it with this path.
- Map every user, gadget, app, and data path.
- Hit high-stakes stuff first, like client records.
- Roll out in waves: Access first, then networks, data.
- Auto-rules via smart networking keep it steady.
- Drill security into everyone.
- Watch metrics: Fix times, blocks, rule checks.
- Team with SASE pros for quick wins.
- CISA pushes this for feds—tweak for business.
Future of Cybersecurity with the Zero Trust
Model
In Cybersecurity It keeps pace with smart hackers. Quantum-proof codes beat tomorrow’s cracks; zero-knowledge tricks verify without spilling secrets.
5G and edge gear widen playgrounds, needing spread-out the trust security. Rules like EU’s DORA force it by 2025.
Gartner says 60% of big outfits go this trust security by 2026, trimming hack bills 30%. As countries amp AI weapons, ot is your best guard.
Grab zero trust security now to lock in the future. Keep eyes open, check everything
